Activity Log / Audit Trail
Every regulator, every auditor, and every infection-prevention surveyor eventually asks the same question: who changed this, and when? clearPath answers it with a tamper-evident system event log. Sign-ins, sign-outs, password changes, role changes, target edits, audit edits, archive actions, and configuration updates are all captured with the user, timestamp, source IP, and the before-and-after value of whatever changed.
The log is queryable from inside the application by users with the right permission, and it's also exportable for offline review. It's the artifact that lets you confidently say yes, we have controls in place when the question comes up at survey.
Request for Information Compare EditionsKey Benefits
- Sign-in / sign-out events
- Configuration changes with before/after values
- Audit edits with full diff
- Role and permission changes
- Source IP captured
- Filter by user, event type, or date
- CSV export for offline review
- Append-only / tamper-evident
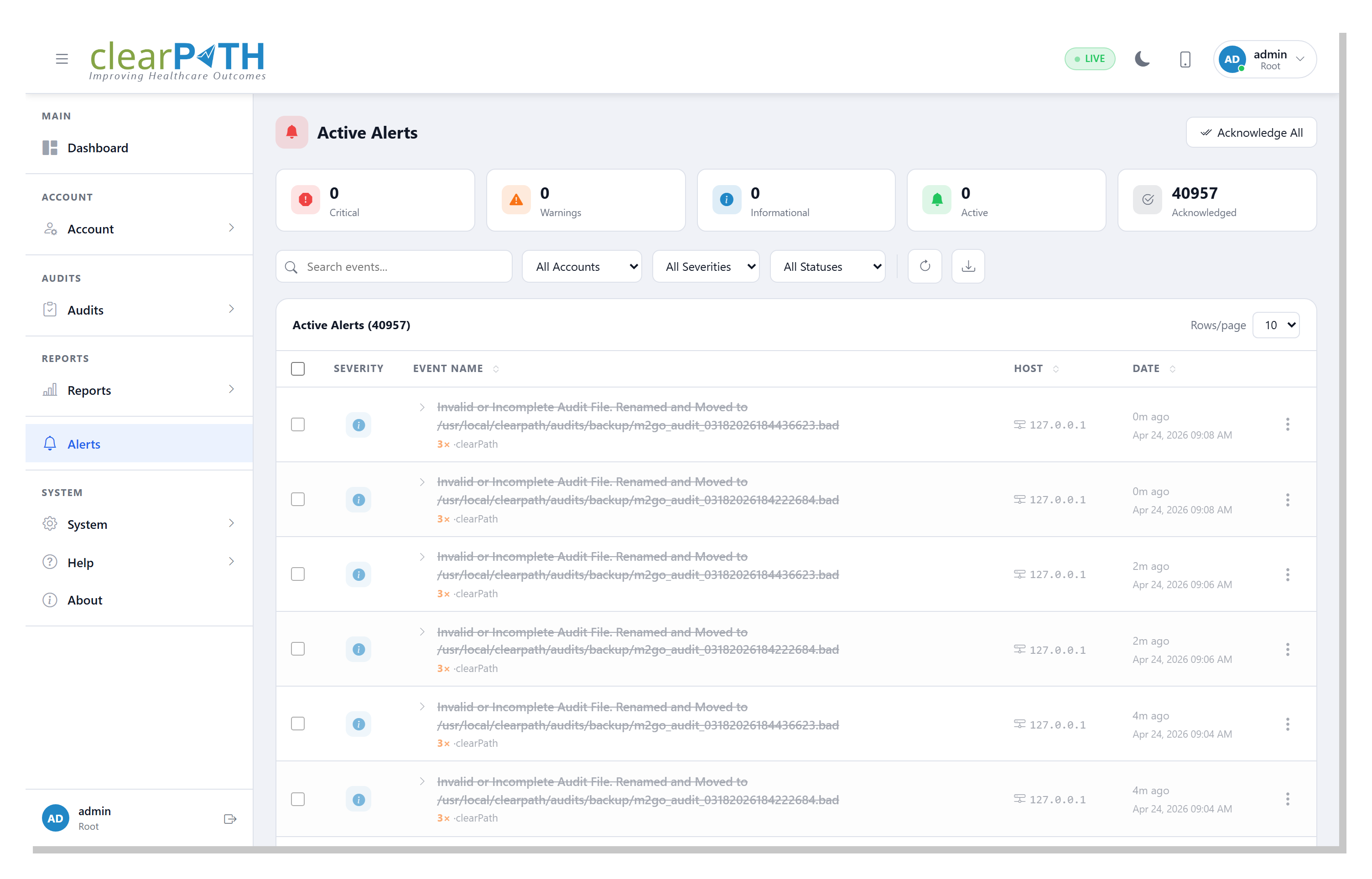
The System Event List
The system event list is the queryable face of the activity log. Every captured event gets its own row with the user, the action, the affected object, and the timestamp. Filter to a specific user to investigate access; filter to a specific record to see its complete change history; filter by date to assemble a survey report. Each row drills down to a full diff of what changed.
- One row per system event
- Per-event drill-down with full diff
- Filter by user, action, or affected record
- Date-range filtering down to the minute
- Direct links from edits to the changed record
Surveyor-Ready Chain of Custody.
Available on Enterprise and Ultimate editions. The activity log is included at no additional cost.
Request for Information Compare Editions